
Hackers Recreated Every Movement of a Damaged Car with Just One Computer Module
BYD
The latest in car news and reviews, without the fluff
Subscribe to our free daily newsletter for the most important stories delivered straight to you every weekday.
Nowadays, it feels almost impossible to escape tracking, whether it’s via your smartphone, computer, various “smart” devices, or even your vehicle. While some may find comfort in still being able to purchase a car without features like navigation or GPS-based emergency services, the reality is that many contemporary vehicles (essentially everything manufactured over the last twenty years) include on-board data recorders—akin to a digital version of the “black box” found in commercial airplanes—and some have the capacity to store extensive tracking data.
Vehicle Privacy: A Brief Overview
Modern cars come equipped with telematics modules that manage communication between the vehicle and various networks, usually including a GPS receiver.
These modules can retain highly detailed data about the vehicle, such as its mechanical status and geographical location.
Importantly, this data can remain accessible even after the module is removed from the vehicle.
In many instances, the data is stored without encryption, which means that if someone gains physical access to one of the car’s modules, they can potentially reconstruct every journey the car has ever taken. A group of ethical hackers demonstrated this using the telematics unit (the module responsible for communications) from a damaged BYD Seal.
They purchased a used module, almost guaranteeing that it retained customer data (since a new car would not have recorded any trips yet). Lacking the correct adapter to read the stored data, they built their own connection to interface it with a USB flash tool—similar to the tuner used to modify fuel maps in a customized car, but without the entire OBDII setup.
“From there, the ubireader tool allowed us to acquire the complete filesystem for the modem, custapp, and system partitions,” the hackers reported. “With the extracted files, we could delve into the root filesystem (rootfs) and user space (usrfs) for intriguing or concealed artifacts.”
And since none of this data was encrypted, accessing it turned out to be quite straightforward.
“By analyzing the GNSS logs, we reconstructed the vehicle's entire history from its manufacturing in a factory in China, through its operational period in the United Kingdom, to its eventual dismantling in Poland,” they stated. “Every movement and halt is documented in the logs, painting a full picture of the vehicle's journey.”
This effort required more than just the chip's data but did not need specialized equipment or access to private databases. Public OSINT tools were sufficient. What is OSINT? It stands for “Open-Source Intelligence,” referring to various methods of gathering information on individuals via the internet without any associated costs.
Using this straightforward two-pronged method, they could correlate unusual data points with real-world occurrences.
“Mapping these coordinates illustrates the vehicle’s complete journey across countries,” they noted. “While most movements aligned with expected routes, during its UK operation we observed a cluster of GPS points in a single location, deviating from normal travel patterns.”
By conducting a simple Google search with specific time and date parameters, they discovered social media posts about a tipped-over BYD Seal involved in an accident, which accounted for the lengthy series of stationary GPS signals. The vehicle was lying on its side.
What data is generally saved in automotive computer modules?
- Time and date: Records of when the vehicle is on, operational, or charging (if it's electric).
- Location data: GPS coordinates logged by the telematics system.
- Vehicle health information: Fluid life (oil/coolant/accessory), engine hours, emission fault codes, and maintenance-related data.
- Accident/event data: Many include a “black box” feature that retains information about the vehicle from the moment of (and just prior to) an accident.
As previously mentioned, automakers (and regulators) have recently begun enforcing stricter encryption practices, and given that the BYD Seal is produced in China, that introduces additional complexities.
However, we are now three decades into the GPS navigation trend, and there is no shortage of older vehicles that could potentially provide valuable intelligence if they were misappropriated. Even Tesla has not been entirely free from similar vulnerabilities, despite the company touting its encryption measures.
The solution? For starters, avoid purchasing a Chinese car. For those in America, this concern may be minimal, but even without that risk, many vehicles likely harbor similar vulnerabilities. The best strategy is to opt for older, budget-friendly cars. Remember, luxury vehicles were the pioneers of this technology.
Have a news tip? Reach out to us at tips@thedrive.com!

Other articles
 Here's What the Recent Changes to the 2026 F1 Regulations Truly Imply
Was it truly essential to adjust the F1 regulations after only three races? It's already been done, and we will soon find out if it leads to the desired outcomes.
Here's What the Recent Changes to the 2026 F1 Regulations Truly Imply
Was it truly essential to adjust the F1 regulations after only three races? It's already been done, and we will soon find out if it leads to the desired outcomes.
 Helmut Marko: Toto Wolff still has an ace up his sleeve.
Former Red Bull motorsport consultant Helmut Marko gave an interview in which he discussed the problems of his former team and mentioned that Toto Wolff's son, who races in karting, has the potential to reach Formula 1.
Helmut Marko: Toto Wolff still has an ace up his sleeve.
Former Red Bull motorsport consultant Helmut Marko gave an interview in which he discussed the problems of his former team and mentioned that Toto Wolff's son, who races in karting, has the potential to reach Formula 1.
 Here’s What the Adjustments to the 2026 F1 Regulations Truly Signify
Was it truly essential to adjust the F1 regulations after only three races? It has been done, and we will soon find out if it produces the desired outcomes.
Here’s What the Adjustments to the 2026 F1 Regulations Truly Signify
Was it truly essential to adjust the F1 regulations after only three races? It has been done, and we will soon find out if it produces the desired outcomes.
 Helmut Marko: Toto Wolff still has an ace up his sleeve.
Former Red Bull motorsport consultant Helmut Marko gave an interview in which he discussed the problems of his former team and mentioned that Toto Wolff's son, who races in karting, has the potential to reach Formula 1.
Helmut Marko: Toto Wolff still has an ace up his sleeve.
Former Red Bull motorsport consultant Helmut Marko gave an interview in which he discussed the problems of his former team and mentioned that Toto Wolff's son, who races in karting, has the potential to reach Formula 1.
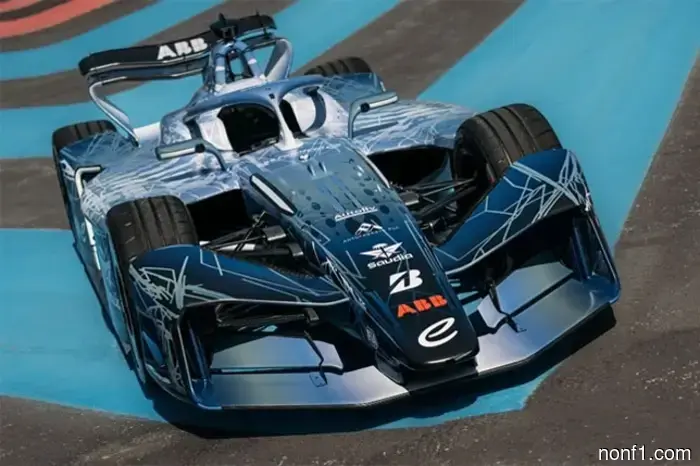 The GEN4 Formula E car debuted on the track.
Today at the Paul Ricard circuit in Le Castellet, the debut of the new generation GEN4 car of the electric Formula E took place.
The GEN4 Formula E car debuted on the track.
Today at the Paul Ricard circuit in Le Castellet, the debut of the new generation GEN4 car of the electric Formula E took place.
Hackers Recreated Every Movement of a Damaged Car with Just One Computer Module
Contemporary vehicles monitor your location not only during navigation but also through onboard electronics that record information about all of your movements.
